Prerequisites
This section describes the prerequisites required for installing TDP Kubernetes. Ensure that all items are met before starting the component installation process.
Infrastructure Requirements
Kubernetes Cluster
- Kubernetes version 1.27 or higher
- Operational cluster with at least 3 node workers (recommended for high availability)
- Administrative access to the cluster via
kubectl
Command Line Tools
| Tool | Minimum Version | Description |
|---|---|---|
kubectl | 1.27+ | Kubernetes CLI, configured for the target cluster |
helm | 3.2.0+ | Kubernetes package manager for chart installation |
Verify the installed versions:
kubectl version --client
helm version
Storage Classes
TDP Kubernetes requires Storage Classes configured on the cluster for dynamic provisioning of persistent volumes.
| Access Mode | Usage | Required |
|---|---|---|
| ReadWriteOnce (RWO) | Used by most components (PostgreSQL, Kafka, ClickHouse, etc.) | Yes |
| ReadWriteMany (RWX) | Required for Apache Airflow (DAG and log sharing between workers) | Conditional |
ReadWriteMany (RWX) mode is required only if Apache Airflow is installed in cluster mode. Solutions such as NFS, CephFS, or Azure Files can provide RWX support.
Verify the Storage Classes available on the cluster:
kubectl get storageclass
HTTP/HTTPS Exposure of Components
An HTTP/HTTPS traffic ingress solution is required to expose the web interfaces of some TDP Kubernetes components, such as Airflow, Superset, ArgoCD, NiFi, and JupyterHub.
Ingress Controller
The environment can use an Ingress controller to publish web services in the cluster.
Common examples:
- NGINX Ingress Controller
- Traefik
- HAProxy
- AWS Load Balancer Controller
Verify whether an Ingress controller is installed in the cluster. Example with NGINX Ingress Controller:
kubectl get pods -n ingress-nginx
Gateway API
The environment can also use Gateway API, provided the cluster has the required resources and a compatible controller already installed.
Example verification:
kubectl get gatewayclass
The Kubernetes Ingress API is frozen and no longer receives new developments. In addition, the Ingress NGINX project was retired in March 2026. The use of an Ingress Controller or Gateway API should follow the strategy adopted for the environment and the implementations supported in the cluster.
Network Configuration
DNS
- Kubernetes cluster nodes must have functional DNS resolution
- It is recommended to configure DNS records for services exposed via Ingress (e.g.
airflow.tdp.example.com,superset.tdp.example.com)
Network Policies
- Ensure that the cluster's Network Policies allow communication between pods in the namespace.
- TDP components need to communicate freely within the same namespace
- If restrictive Network Policies are in place, configure rules that allow ingress and egress traffic between TDP pods
TLS/SSL Certificates (Optional)
To enable HTTPS on services exposed via Ingress:
- Provision TLS/SSL certificates for the configured domains
- Use cert-manager for certificate automation with Let's Encrypt or an internal CA
- Configure the certificates on the Ingress resources of each component
OCI Registry Authentication
- Instructions
- Web Registry Login
- CLI Secret Retrieval
- Registry Login via Helm
-
Access the Tecnisys registry and obtain your command-line credential (CLI Secret / access token).
 Figure 1 – Web Registry Login
Figure 1 – Web Registry Login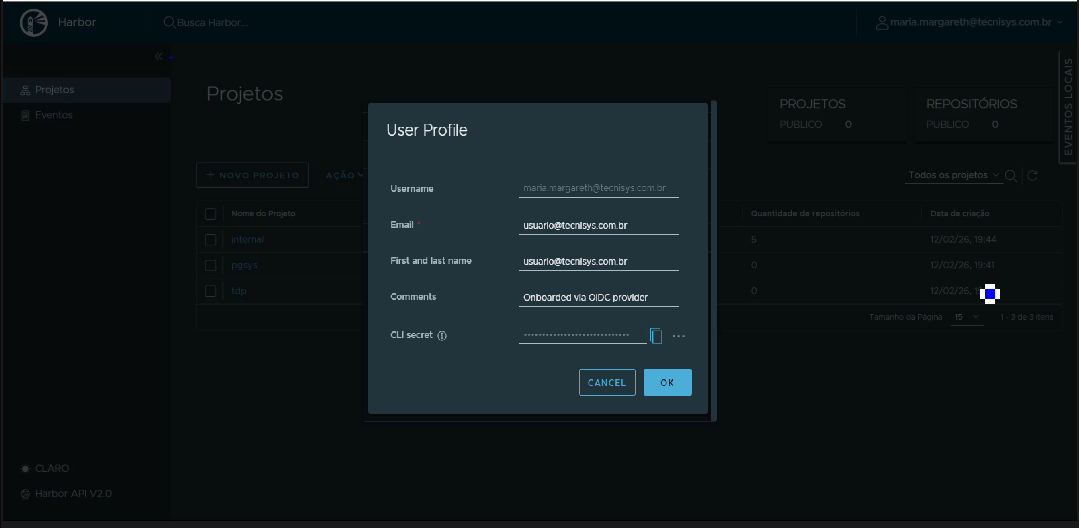 Figure 2 – CLI Secret capture
Figure 2 – CLI Secret capture -
Authenticate Helm with the Tecnisys OCI registry to access the platform charts.
Terminal inputhelm registry login registry.tecnisys.com.br -u <user@tecnisys...>When you run the command, the terminal will prompt for the password:
Password:At this point, enter the CLI Secret / token obtained from the registry.
If authentication completes successfully, Helm will display a login confirmation and you will then be able to query and install the charts available in the registry.
Registry access credentials must be obtained from Tecnisys. If you do not yet have access, contact the responsible team to request your authorised user and CLI credential.
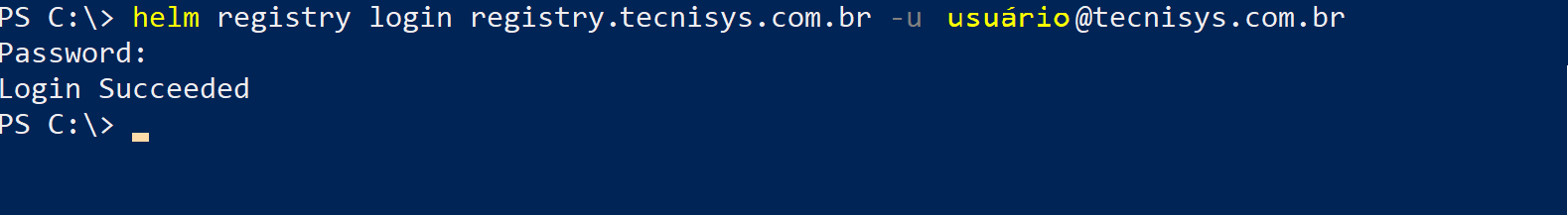 Figure 3 – Registry Login via Helm
Figure 3 – Registry Login via Helm -
After authentication, verify access by listing a sample chart:
Terminal inputhelm show chart oci://registry.tecnisys.com.br/tdp/charts/tdp-spark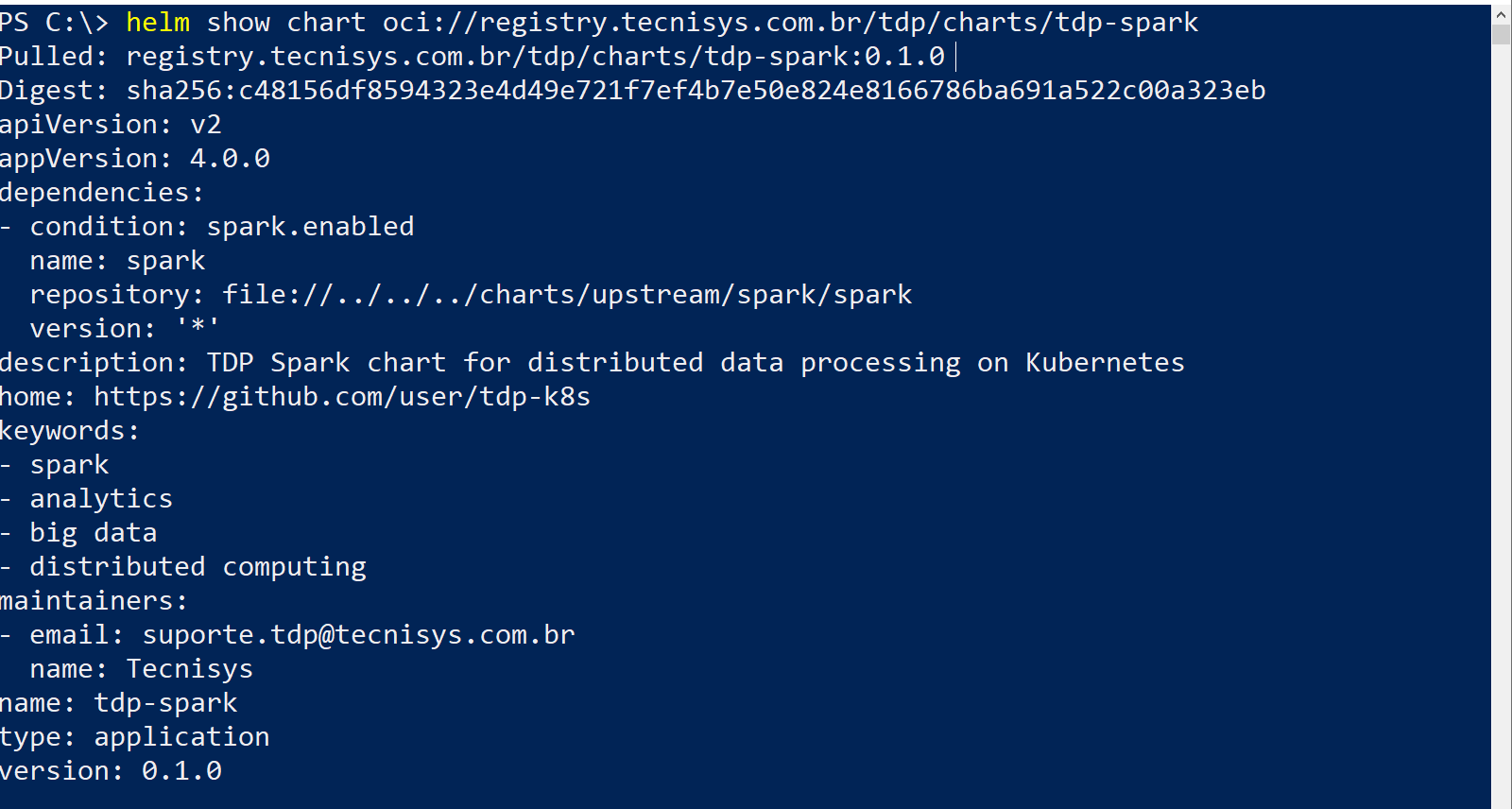 Figure 4 – Show chart – example
Figure 4 – Show chart – example
Verification Checklist
Before proceeding with the installation, confirm all items below:
- Kubernetes 1.27+ cluster operational
-
kubectlconfigured and connected to the cluster -
helm3.2.0+ installed - Storage Class with ReadWriteOnce support available
- Storage Class with ReadWriteMany support available (if installing Airflow in cluster mode)
- HTTP/HTTPS ingress solution (Ingress Controller or Gateway API) installed and operational
- Sufficient computational resources on cluster nodes
- DNS resolution configured for nodes
- Registry authentication (
helm registry login registry.tecnisys.com.br) completed successfully - TLS/SSL certificates provisioned (optional)